TECHNOLOGIES
CODIKETT 2.0 | OUR TRACEABILITY SYSTEM

TECHNOLOGIES
OUR TRACEABILITY SYSTEM
KEY BENEFITS OF OUR IOT PLATFORM CODKIETT 2.0
CLOUD-NATIVE PRODUCT SECURITY WITH REAL-TIME ANALYTICS
Codikett 2.0 is not a “QR project”, but a platform approach: secure digital identities (UIDs), controlled data views, and analytics that turn scan events into decisions. Organizations that integrate product protection, traceability, and upcoming data compliance requirements into a unified strategy reduce tool fragmentation — and gain speed.
The cloud-native platform connects secure UID generation with real-time analytics, role-based data access, and enterprise integrations. It enables scalable product authentication, end-to-end traceability, and intelligent brand protection within a unified Track & Trace Plattform architecture.
WHY PRODUCT PROTECTION IS A PLATFORM QUESTION
Counterfeiting is no longer just a brand issue; it is a structural supply chain risk. According to estimates by the Organisation for Economic Co-operation and Development (OECD) and the European Union Intellectual Property Office (EUIPO), global trade in counterfeit goods reached approximately USD 467 billion in 2021, representing around 2.3% of global imports.
The impact extends beyond lost revenue. It affects patient safety, warranty and recall costs, regulatory compliance, and the integrity of distribution networks.
At the same time, regulatory frameworks increasingly require transparency, structured product data, and verifiable processes. Many organizations respond with isolated tools: standalone QR codes, disconnected portals, spreadsheets for partners, manual audit reports. These approaches do not scale.
What is missing is a consistent digital layer between the physical product, its secure identity, and the differentiated data access required by multiple stakeholders.
STRONGER PRODUCT SECURITY, CLEARER INSIGHTS - AND BUILT FOR INSTANT "WOW".
WHAT CODIKETT 2.0 DELIVERS
Codikett 2.0 links non-guessable Unique Identifiers (UIDs) with real-time analytics and role-based access rights – enabling product authentication, traceability, and grey market detection within a secure, single tenant architecture.
It is not a “QR project.” It is an integrated Anti-Counterfeiting Software and Track & Trace platform.
01
Secure UID Generation instead of “Just a Code”
The distinction between a generic QR number and robust product security lies in the UID strategy.
Core principles of UID Generation in Codikett 2.0:
- Unpredictability and non-enumerability – UIDs cannot be trivially guessed or incremented.
- Lifecycle logic – UIDs align with batch, serial, country, channel, or campaign structures without constant artwork changes.
- Verifiable integrity – Each authentication event is traceable without compromising data quality (e.g., separation of test vs. live scans).
In Codikett 2.0, the UID is the anchor for authentication, Track & Trace processes, analytics, and downstream workflows.
02
App-Free Verification with Dynamic Response Pages
A scan event only creates value if it generates a clear and secure response.
Codikett 2.0 enables differentiated outputs through role-based access rights:
- Consumers receive simple authenticity confirmation and product information.
- Distribution partners see additional process data, potentially in localized views.
- Internal roles (QA, inspection, compliance) access extended diagnostic interfaces.
A dynamic response-page designer allows rapid updates in brand-compliant design without reprinting packaging. The digital layer evolves while the physical carrier remains unchanged.
03
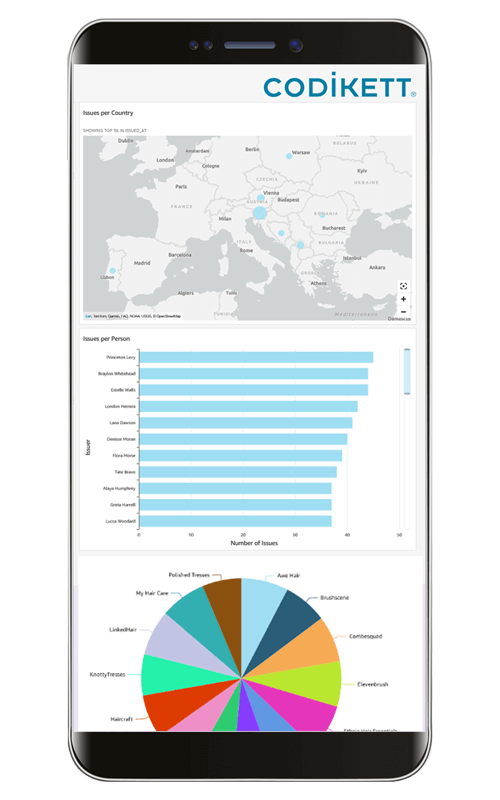
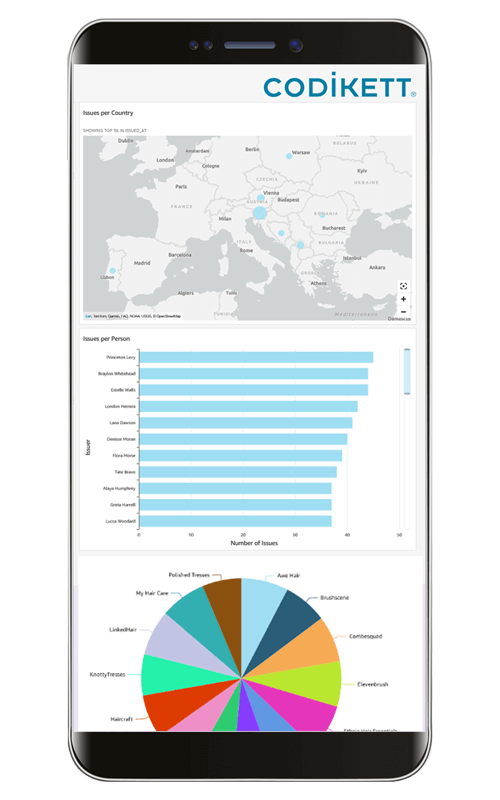
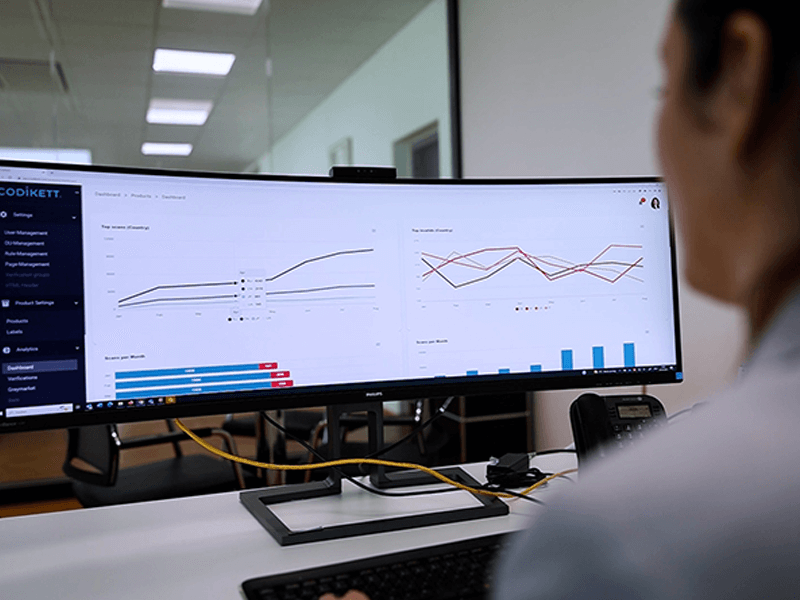
Real-Time Analytics: Turning Scan Events into Signals
Many Track & Trace initiatives fail not at labeling but at analysis.
Typical operational questions include:
- Where do scans cluster outside intended markets?
- Which batches show anomalous verification patterns?
- Which partners or regions require alerts?
- What constitutes a statistical outlier?
Codikett 2.0 provides live analytics dashboards, UID statistics, and verification insights. This transforms raw scan data into actionable intelligence – supporting brand protection, compliance, and distribution control.
04
Governance, Single Tenant Isolation, and Integrations
As ecosystems expand – CMOs, distributors, retailers, service partners – data governance becomes critical.
Codikett 2.0 addresses this through:
- Role-based access rights with granular permission models
- Single Tenant isolation for secure participant and data separation
- API-based integration into ERP, WMS, CRM, and PIM systems
The objective is not to operate another portal, but to embed authentication and Track & Trace events into existing enterprise workflows.
SIMPLE, QUICK, ONLINE
LET’S CONNECT DIGITAL AND PHYSICAL SECURITY

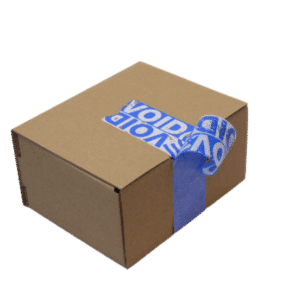
Codikett offers a modular architecture for all digital product security requirements. From our portfolio, we assemble the right package to protect products against fraud and counterfeiting, facilitate consumer communication, and manage distribution channels.
Our system combines highly secure UIDs, based on cryptographic methods along with a variety of physical security features. This approach ensures robustness against copying by using tamper-proof labels that utilize VOID technology, covert hash codes, and various overt and covert security features.
CORE USE CASE
WITH IMMEDIATE BUSINESS VALUE
PRODUCT AUTHENTICATION & BRAND PROTECTION
- Consumer authentication at point of sale or use
- Distributor and partner verification
- Pattern recognition for suspicious serial clusters
- Centralized Anti-Counterfeiting Software control layer
GREY MARKET DETECTION & DISTRIBUTION INTELLIGENCE
- Scan events in unintended regions
- Repeated verification of identical UIDs
- Channel-specific alerting (e.g., online marketplaces)
- Data-driven distribution monitoring
TRACK & TRACE, TRACEABILITY & RECALL READINESS
- Batch and serial-level logic for targeted recalls
- Verifiable event chains
- Role-specific communication (public vs. authority vs. partner view)
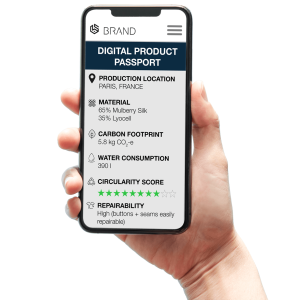
DIGITAL PRODUCT PASSPORT (DPP) ENABLEMENT
- Role-based DPP frontends (public, authority, partner)
- Data integration from ERP and PIM systems
- Standards connectivity (e.g., GS1 Digital Link / EPCIS depending on project scope)
Codikett 2.0 positions your Track & Trace Plattform as a structured foundation for future regulatory requirements.
CODIKETT 2.0 IMPLEMENTATION ROADMAP
90-DAY STRUCTURED ROLLOUT

Phase 1: Minimal Viable Rollout
- UID strategy and label concept
- Initial verification flow
- First response page
- Baseline analytics (scan count, time, region)
Phase 2: Roles & System Integrations
- Definition of role models (consumer, partner, QA)
- API integration with core enterprise systems
Phase 3: Scaling & Standardization
- Multi-market rollout
- Interoperability setup (e.g., GS1 Digital Link)
- Advanced workflows (recall management, DPP views)
PROJECT CHECKLIST BEFORE LAUNCH
- Primary use case: Product authentication, grey market detection, traceability, or DPP
- Carrier technology: QR, DataMatrix, NFC, or RFID
- UID granularity: model-level, batch-level, or item-level
- Role and data views: public vs. internal vs. partner
- System integrations: data sources and event consumers
- Operating model: deployment, SLAs, support, governance parameters
A structured definition phase reduces project complexity and prevents fragmented implementations.
FAQs ABOUT CODIKETT
Codikett is Securikett’s digital platform for product traceability, verification, and authentication using unique identifiers (UIDs).
Product digitalization means giving every product its own unique code. This code is printed or applied on the item and links to a digital record. In this record, information such as product details, production data, logistics steps, or regulatory content like a Digital Product Passport can be stored. To make this work, companies need to choose how codes are applied (print, label, packaging), ensure integration on the production line, connect the system with ERP or MES, and handle data securely. It is also important to define clear responsibilities for data ownership and to make sure all partners in the supply chain follow the same standards.
Product digitalization involves connecting a product to information in the cloud using a unique code for each item. Digitalization offers several key benefits: it enhances supply chain transparency through real-time tracking and data-driven decisions, improves efficiency and reduces costs, and boosts consumer engagement by enabling personalized experiences and direct communication channels, thereby fostering brand loyalty.
Today, product digitalization is an indispensable component to all anti-counterfeiting measures, which typically includes copy-proof technology and tampering verification features.
Product digitalization enables detailed data collection and analysis, providing insights into consumer behavior and market trends for strategic decision-making. It streamlines regulatory compliance by ensuring accurate and accessible documentation throughout the product lifecycle.
When using Codikett UIDs, a planned distribution chain is assigned to each product. By scanning the codes, distributors, consumers, and other users provide feedback on whether the products are in the correct market.
a. Grey trade will be unveiled immediately.
b. Packaging aggregation is one of the possible methods for assigning destinations.
Every participant can log in to Codikett and download their own UIDs in custom formats, typically CSV. The brand owner always has full visibility on who issued which codes and when. For automated use cases, UIDs can also be provided via API, so they can flow directly into printers, ERP systems, or partner workflows.
Codikett records verification and process events within seconds. Dashboards update continuously, and optional webhooks provide instant notifications. This allows near real-time tracking across production, logistics, and market activities.
Real-time data is also used to create alerts in case of fraudulent activities within the market.
Codikett provides information that can be used across different areas. Scan data shows where and when products are verified, which can reveal unusual market activity. Production and packaging records help to compare planned and actual quantities, while logistics events make product movements visible. Time-based comparisons support the identification of irregularities and help in coordinating supply chain and quality processes.
Scan the QR code on the product’s security label with your smartphone to access the verification page and check the validity of the Unique Identifier. You will then receive further information on the product and its authenticity.
Yes, customers do scan the codes. Our software encourages scanning through features like gamification (e.g., slot machines and giveaways), interactive product information, and engaging content.
Securikett’s labels are designed to attract attention with their appealing designs. Codikett features, such as a hidden pin, additionally attract users while providing security against code cloning. These features work together to increase consumer interaction and engagement with the codes.
Scan volumes are displayed in the Codikett analytics dashboard. Users can customize dashboards to focus on specific products, regions, or periods. Reports can be scheduled or exported, and time-frame comparisons help to identify trends or unusual activity.
Yes, Codikett is available globally. You can track and verify products internationally, ensuring security and engagement with consumers no matter their location.
Codikett features intuitive interfaces that simplify use, customizable frontends tailored to production needs to ensure users only see relevant information, and role-specific views that allow different users to interact with data pertinent to their responsibilities, thereby enhancing productivity and usability.
Yes, Codikett is designed to meet the requirements of the Digital Product Passport for each industry sector. Two options are available, depending on industry requirements and public infrastructure. One option is to display DPP information directly in Codikett, and the other is to provide interoperability with a third-party industry provider.
The number of users is flexible and tailored to your needs. You can manage user roles independently through the Codikett platform, assigning specific permissions for different roles such as administrators, operational personnel, distributors, and inspectors. This allows you to control access and functionalities based on users’ responsibilities.
No, the displayed information is specially selected based on user roles, ensuring that only relevant and permitted data is shown to different stakeholders.
Codikett uses a modular pricing structure tailored to specific needs and the scale of implementation. Costs depend mainly on the number of unique codes issued and the modules in use. A pilot can start with a small SaaS fee and setup, while large-scale rollouts scale with volume and features such as analytics, CMO control, or digital product passports. This way you only pay for what you actually need.
For a detailed and customized pricing plan, please contact our sales team.
Codikett can be connected to and communicate with existing systems, including SAP/ERP and CRM, using customized APIs.
Yes, you can start with a small implementation of Codikett for a limited number of products or batches and gradually extend its use as your needs grow. You can begin with basic product verification and later expand to full track and trace capabilities or grey market detection as your requirements evolve. Additionally, you can initiate implementation in one part of your company or organization and gradually expand to more affiliates or Contract Manufacturing Organizations (CMOs).
Codikett detects market fraud by analyzing verification data for duplicate scans, out-of-market scans, impossible travel, burst patterns, and many more, then surfaces hotspots on geo heatmaps and triggers alerts for fast brand protection action.
The solution is built for peaks. a cloud-native, autoscaling architecture keeps verification and response times low even during high-traffic campaigns or DDOS-Attacks.
The simplest way to use Codikett is through internet access and a browser. Many clients also provide a domain or subdomain and set up a CNAME for branded verifications. Single sign-on can be added to connect existing identity systems. For automated use, Codikett offers APIs that allow integration with ERP, MES, or other platforms. Depending on the application, the setup can range from almost no IT effort to a more complex connection of multiple systems.
For a typical traceability solution you need at least a way to apply the code or label, a device to scan and record codes, and often hardware to print shipping labels. Many customers already have suitable printers or scanners that can be incorporated, so additional investments are often minimal. Codikett itself runs without mandatory proprietary hardware.
Yes, Codikett supports RFID and NFC. They can be combined with other features such as QR codes, holograms, or tamper-evident seals on the same product. This enables hybrid solutions where RFID or NFC streamlines logistics and warehouse handling, while tamper loops provide physical protection and authentication
Data is hosted in EU cloud regions by default, encrypted at rest, with strict tenant isolation. Alternative regions are available on request to meet your data residency and compliance needs.
Many clients start with a minimal setup, such as basic product verification or simple code management. As their needs grow, they extend Codikett step by step into areas like track & trace, CMO control, or digital product passports. This phased approach is common across our diverse customer base.
Yes, we support reader implementation ourself or with partners as an end-to-end solution, we scope devices, coordinate with our integrator, and commission cameras, scanners, and printers with Pilots, training, and acceptance tests.
Digital solutions help to identify and reduce grey market and counterfeiting activities. Codikett makes diversion visible, supports authentication, and provides actionable data. Several customers have already used this to significantly reduce grey market volumes.
Product digitalization can be implemented in very different timeframes. A scaled-down pilot can be up and running within two weeks, while a full rollout across sites and systems may take considerably longer. The key is to involve all stakeholders from the start and agree on scope, processes, and data ownership. Beginning with a pilot allows companies to test the setup in practice and then extend step by step as requirements grow.
Codikett allows you to manage CMOs by distributing codes in controlled batches, similar to a tax stamp system. For example, a defined quantity of codes is allocated to a production order, and only this amount can be used. Each code is tracked from issuance to application, so you can see exactly how many products were produced and detect if codes are unused, duplicated, or misapplied. This gives transparency over production volumes and helps ensure that CMOs follow agreed limits.
Yes, if the QR codes are generated as dynamic links. In this case the code itself stays the same, but the target URL behind it can be updated at any time. This makes it possible to adjust landing pages, campaigns, or product information even after packaging is already in the market.
Yes, Codikett can work with existing identifiers if they are unique and of sufficient quality. Codes can be imported in formats such as CSV or JSON and loaded into the system, so you do not need to change your current identifiers. This also applys for Shipping Codes on outer packages.